BRATA malware: An evolving, consistent, and advancing threat

BRATA is an Android mobile malware that is a rapidly evolving, feature-packed banking trojan. It is capable of abusing the accessibility service permissions that are generally needed when a person is in the installation phase. The software is known to have received numerous upgrades and changes to elude detection and allow the threat actors to track the user’s activity on the device.
In the recent discovery, the malware is said to have the capability to operate as an Advanced Persistent Threat (APT), which means the attacker stays on the target network for an extended period and steals sensitive information from it. In addition to that, the malware has updated the phishing techniques that allow it to request additional permissions on the device, which helps the threat actors to send and receive SMS messages and obtain temporary codes such as one-time passwords (OTPs) and two-factor authentication (2FA) that banks send to their clients. As an advantage, the upgrade can minimize the network traffic and the interactions that have to be done with the host devices.
BRATA was first discovered in the wild near the end of 2018 when it impersonated itself as anti-virus software. The application was capable of attacking financial institutions using tailored malware with features that facilitated it to clone the login page of the compromised institution, extract credentials, and get hold of the SMS messages sent to the client.
When it was detected again in 2021, the application gained the capability to operate directly on the victim devices without the need for a new device, which helped them reduce the possibility of seeming suspicious as the device is already known to the bank.
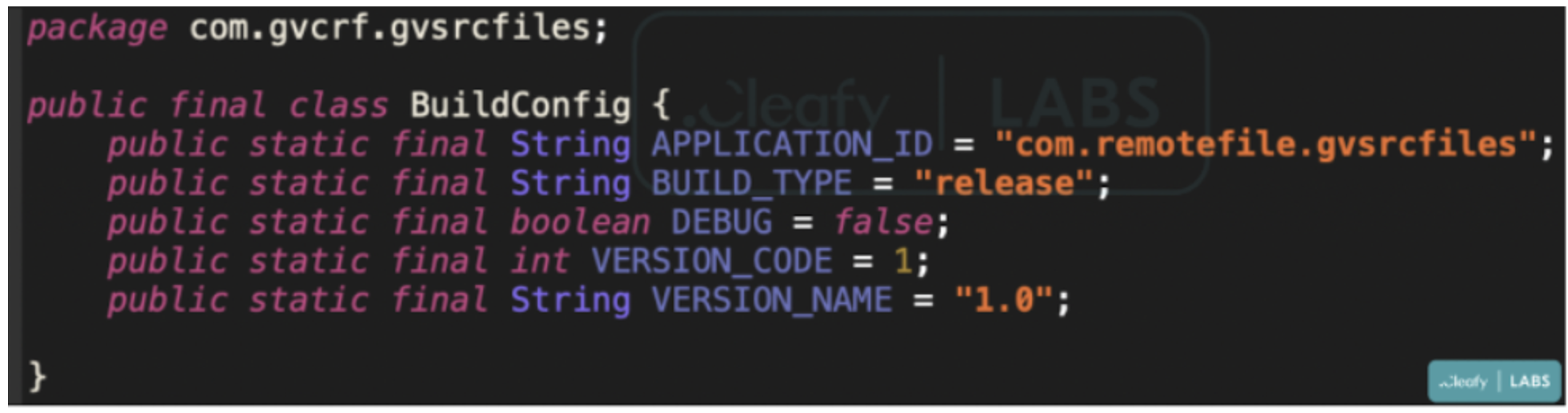
In one of the recent discoveries made in late January of 2022, the application came with an updated feature where it was capable of recording keystrokes, tracking device location, supporting multiple C2 communication channels, and even advancing to perform a factory reset that would help them cover up the wire transfers. The details provided by researchers at Cleafy mentioned that this particular variant was distributed through a downloader that could help them avoid being detected by security software.
How it works
BRATA is propagated using smishing messages that spoof a bank and include a link to a malicious website where the user is fooled into downloading an anti-spam application. The attackers then phone the victim and use social engineering techniques to persuade them to install the trojan software and grant it elevated permissions.
According to the research, the upgrades made in the early months of 2022 enabled the attackers to tempt victims into installing the downloader application. As the victim clicks on the install button, the application sends a GET request to the C2 server to download the malicious APK file.
But in recent reports, BRATA has gained the ability to fetch a ZIP archive from the C2 server that contains the JAR package. The JAR file worked as a sideloaded payload that could log events to the remote server from the compromised device. Moreover, in those instances, if the victim failed to detect the abnormalities, it could turn into an Account Takeover (ATO)attack. Along with the advancement, its keylogging functionality helps track app-generated events and records them locally on the device along with the text contents and a timestamp. If the malware is not alerted or worked upon, it has the capability to lure victims into its web and steal sensitive information from them.
Workaround
Certain measures can be taken to avoid falling victim to the threat. Maintain device updates. If installation from unknown resources has not been disabled yet, it must be done so. Software and applications should only be updated with tools provided by authenticated developers. Having an anti-virus and anti-spyware scanner would work as a plus point to run regular scans to detect such potential threats.
References
https://www.cleafy.com/cleafy-labs/mobile-banking-fraud-brata-strikes-again
https://www.cleafy.com/cleafy-labs/how-brata-is-monitoring-your-bank-account
https://www.cleafy.com/cleafy-labs/brata-is-evolving-into-an-advanced-persistent-threat