Ensuring Secure Online Presence
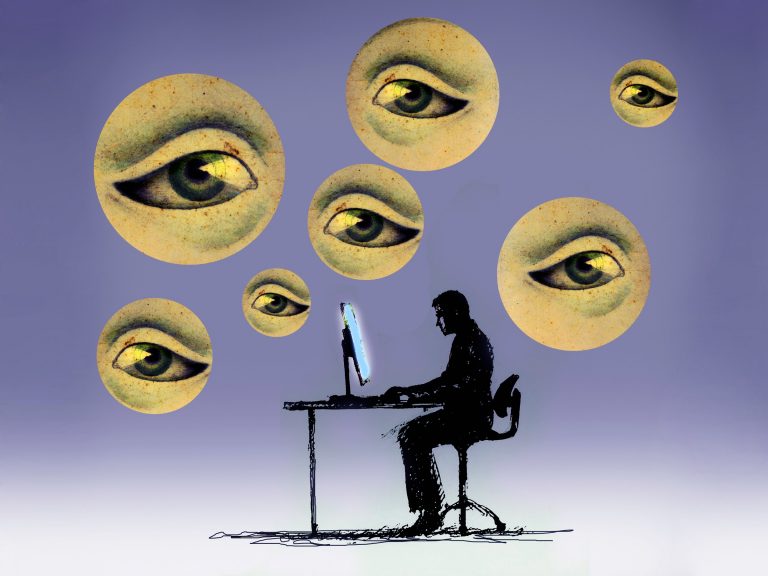
The recent scandal of Facebook’s user data being harvested for use for election manipulation by Cambridge Analytica has brought the issue of data security to wider public discussion. Our private data entrusted to an entity with assurance and expectation of confidentiality being exploited by a third party for nefarious purposes should obviously elicit a strong response. But, we should also consider our part and our negligence that has directly contributed to this. It is our own nonchalant attitude towards the value of our own data that has allowed other parties to obtain and use them with such ease. We publicly disclose our information online that we would not be willing to share with a stranger in real life. This is because we fail to realize that online world is an extension of the real world and think our real life is detached from our digital life. This makes people not pay heed to the potential consequences of being careless with their online presence. We even do not read the terms of services in websites and software which are essentially a binding legal contracts. While we obsess over physical contracts and devote our resources to making sure everything is right, in case of online or digital contracts we just hit the “I agree” button without actually reviewing what is included in it.
The possibility of election fraud is quite substantial in Nepal as well. If you have published your birthdate somewhere on the Internet, then that’s all an attacker needs to extract your voter identity details. The online portal provided by the election commission of Nepal only needs your birthdate before it throws all your private information to the public. We have already written about this in detail in our Threat Report 2017.
We have made a list of steps that you should follow in order to keep your data and yourself safe. We recommend that you follow these steps to stay secure:
- We do not recommend you share your private information anywhere on the Internet unless it is absolutely necessary and you completely trust the website. Such website should be secured with HTTPS protocol.
- Be attentive of EULA and, terms and conditions for software you use and websites you signup to. While reading these long legal documents can be rather demanding, services like tosdr.org can be useful.
- Make sure that private information that you have provided on social media is not sensitive and publicly visible.
- Be very suspicious of apps asking for authorization to your private information
- Do not allow any apps to access your online profiles unless necessary and the app is from trusted vendor
- Be critical of information you provide even to trusted and well known websites
- If using VPN services make sure your IP, DNS or other traceable information is not leaking via the use of services like https://ipleak.net
- Only use genuine software
- Regularly update your systems
- Be very skeptical of random pop-up windows, error messages and attachments
- Make sure you use different passwords for each of your accounts.
- Use strong passwords that can’t easily be guessed. Use password managers such as lastpass and 1password to make it easy to use strong password and store them securely
- Always log off if you leave your device
- Use two factor authentication where possible
- Think twice before clicking on any link you receive in emails or private messages.
- Never trust an email that’s too good to be true
- Keep your antivirus and spyware detection software up to date.
- Use Ad blocker in browser
- Install nominer addon to block cryptojacking
- Enable Popup blocker in browser
- Never download and install unwanted and suspicious media-player/antivirus/games from untrusted sources
- Don’t pick up and plug in pendrives that you just find lying around.
- Never torrent or download cracked games/windows/software from untrusted sources, as most of them have been modified to perform malicious actions.